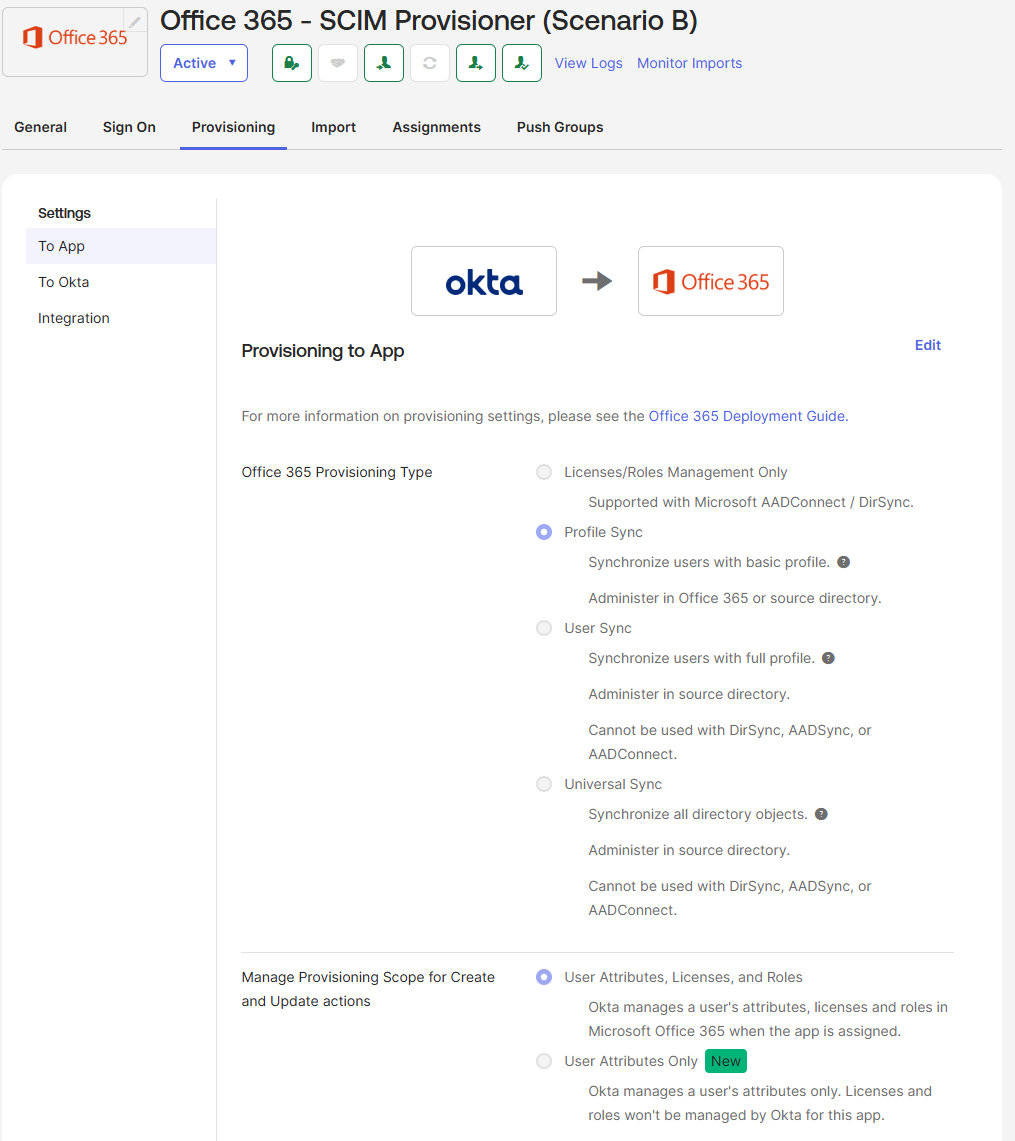
Scenario A
Entra ID as Source of Truth
Entra ID is the authoritative identity store. Okta sits in the middle as a broker, receiving authenticated identities from Entra via OIDC and federating them downstream to Salesforce via SAML. Okta also handles SCIM provisioning to Salesforce, so the full user lifecycle flows through Okta's provisioning engine. This is the Microsoft-first pattern: Entra enforces the access gate and Conditional Access policies, Okta adds SaaS brokering capability on top.
Scenario A: Entra as IdP, Okta as broker, Salesforce as SP
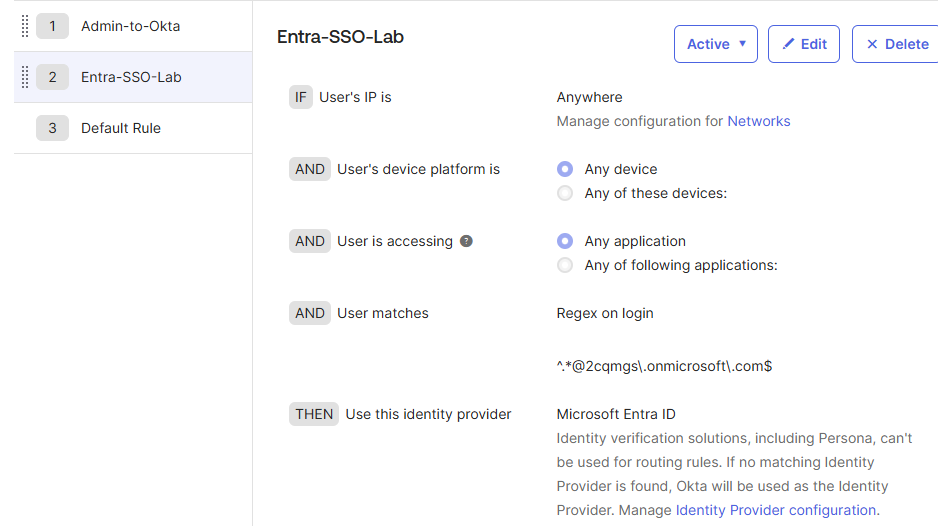
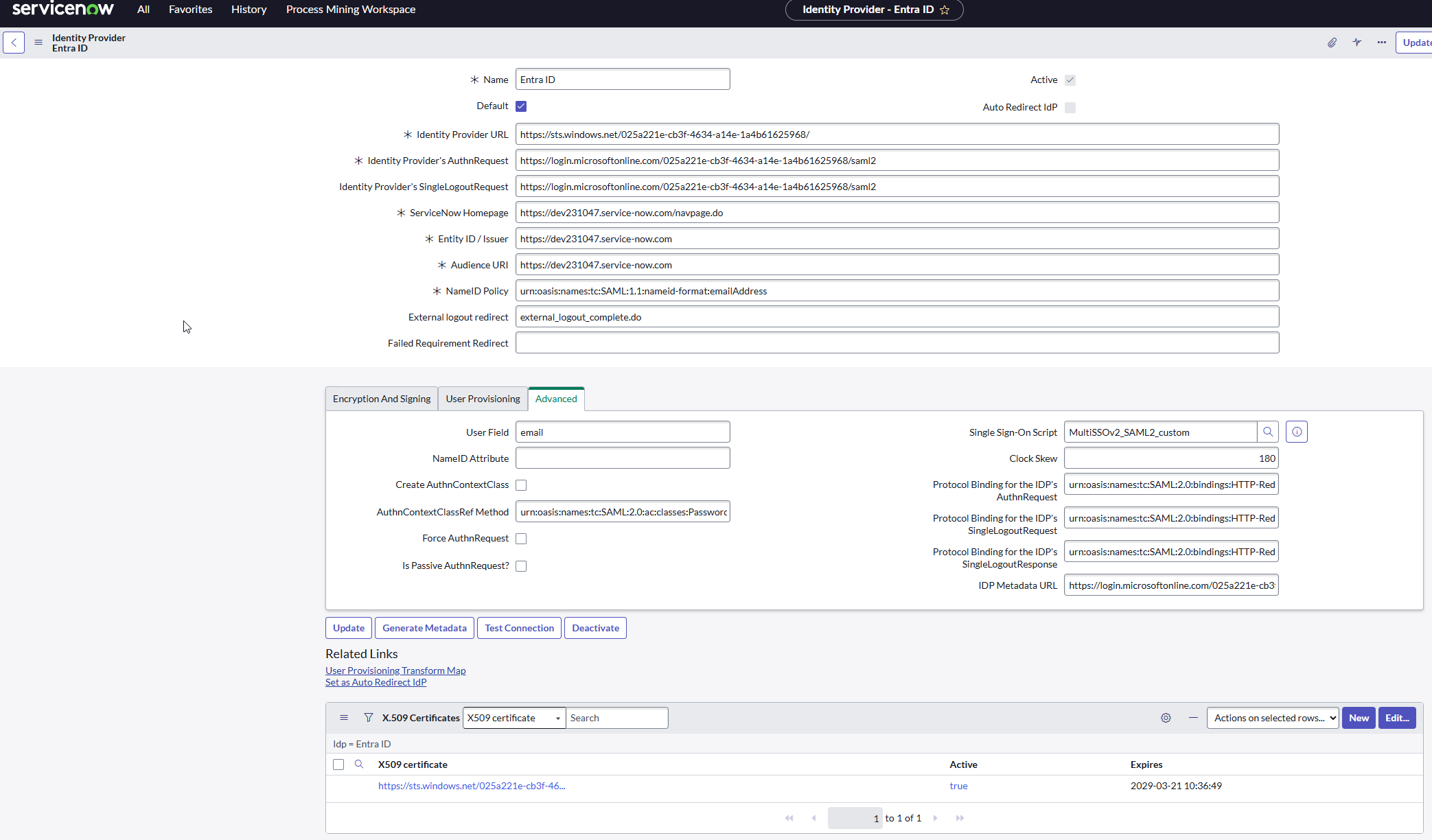
Okta routing rules — admin bypass pinned to position 1, domain redirect rule below. Prevents lockout before federation is live.
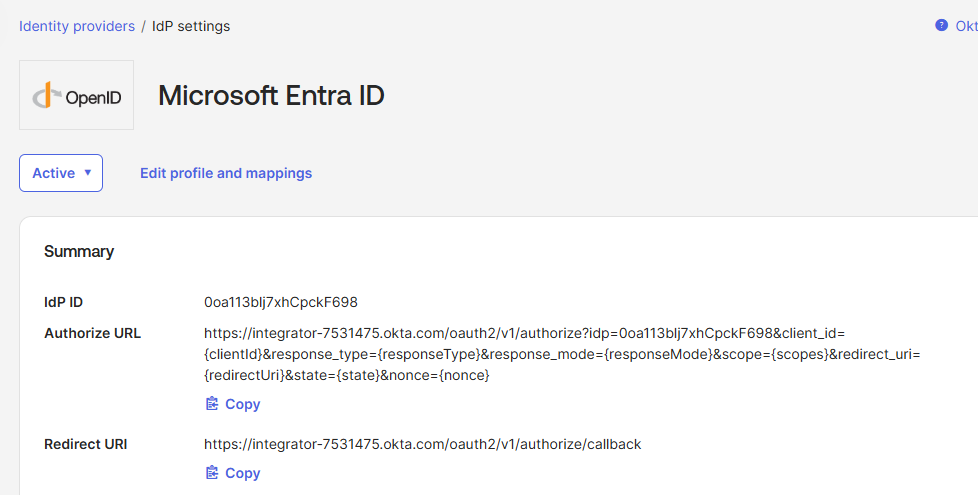
Okta Identity Providers showing Microsoft Entra ID as Active with OIDC / JIT provisioning configured.
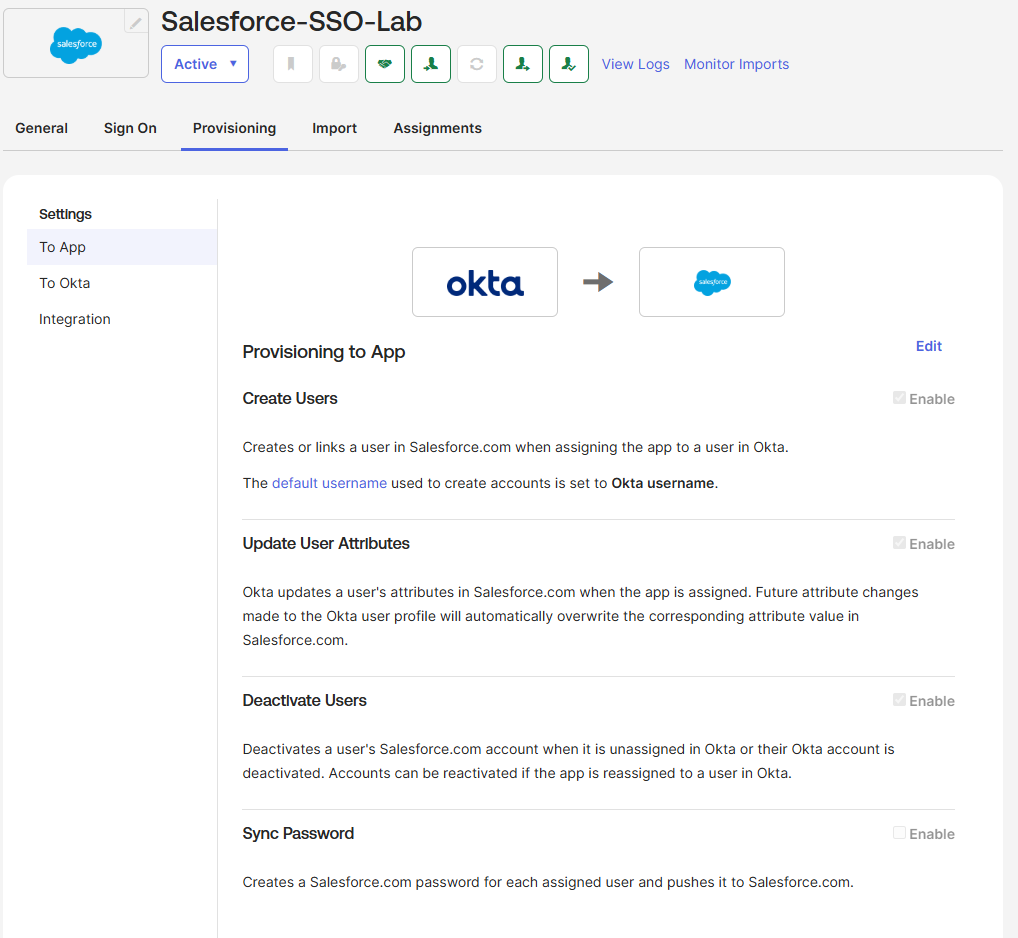
Okta → Salesforce provisioning tab showing OAuth-based SCIM configured with Create, Update, and Deactivate enabled.
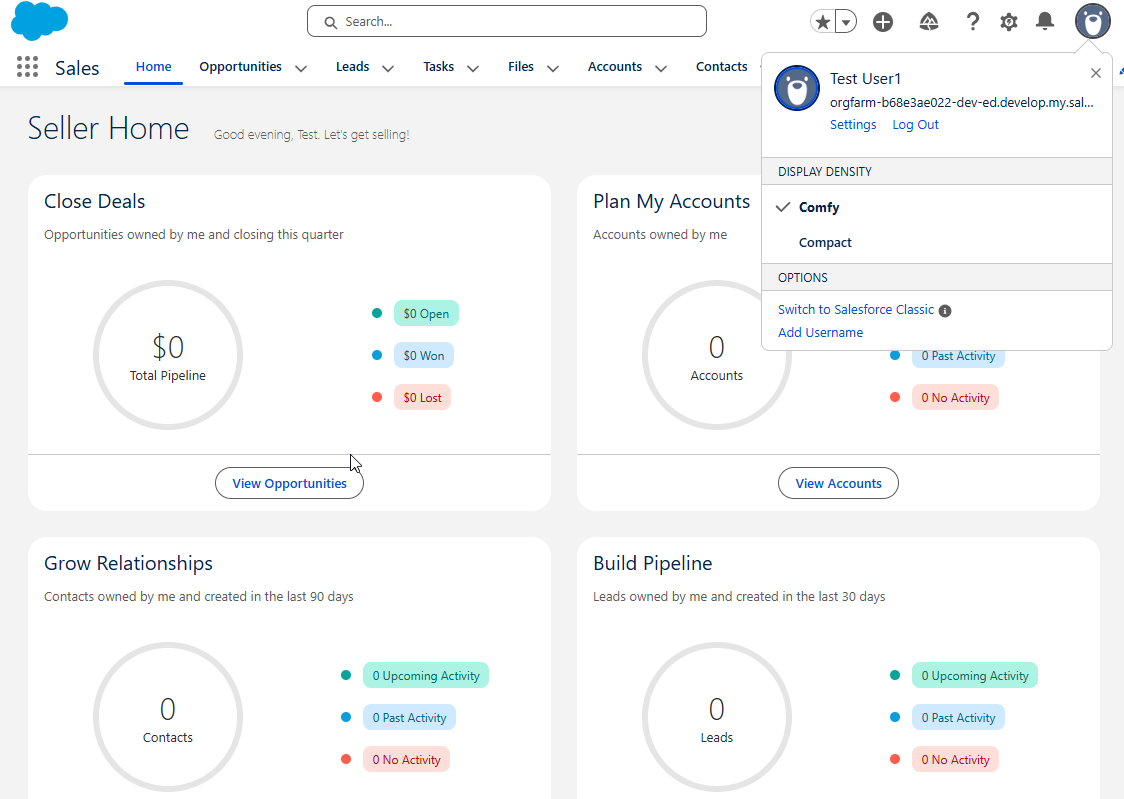
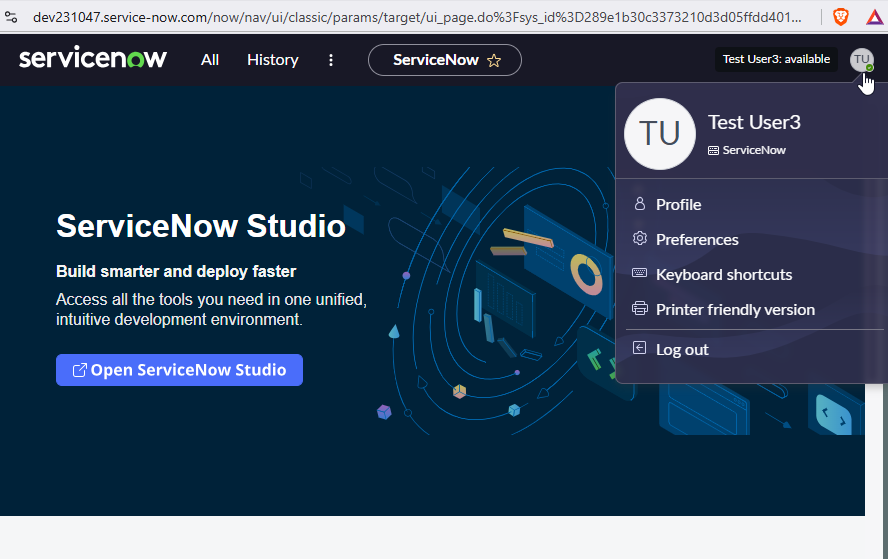
Salesforce login session confirming end-to-end federated SSO through the Entra → Okta → Salesforce chain.